WireGuard is a modern VPN protocol that creates encrypted tunnels using a radically smaller codebase than its predecessors. Where OpenVPN runs on over 100,000 lines of code, WireGuard achieves the same core function in approximately 4,000 lines - a difference that produces measurable speed advantages and a substantially smaller attack surface. First merged into the Linux kernel in version 5.6 (April 2020), WireGuard has since been adopted by NordVPN, ExpressVPN, Mullvad, ProtonVPN, and most major VPN providers as their primary or recommended protocol.
What Is WireGuard?
WireGuard is an open-source VPN protocol designed to be faster, simpler, and more secure than OpenVPN and IKEv2. It operates at the network layer, creating a peer-to-peer encrypted tunnel between two devices without requiring a traditional client-server certificate infrastructure.
It handles how VPNs create encrypted tunnels differently from older protocols by treating every endpoint as a peer rather than designating strict client and server roles. This design simplifies configuration significantly and enables faster reconnection when switching networks - for instance, moving from Wi-Fi to mobile data.
How Does WireGuard Work? (Technical Overview)
WireGuard establishes a connection through a lightweight handshake and then maintains a persistent tunnel for all subsequent traffic. The process differs from OpenVPN in one critical way: there is no separate TLS negotiation phase and no certificate authority required. Each peer has a public key, and connections are authorized by adding a peer's public key to your configuration.
For a broader understanding of VPN encryption protocols explained, WireGuard fits into the category of modern protocols that prioritize minimal overhead. Its connection flow works in four steps:
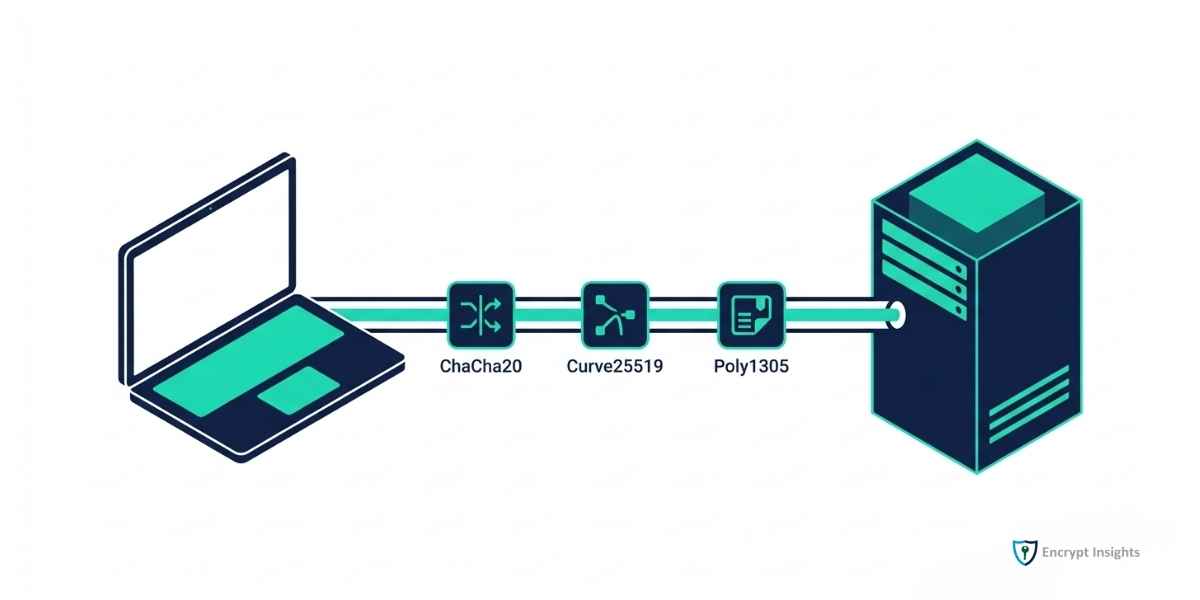
- Key exchange: Both peers exchange Curve25519 public keys. This uses elliptic-curve Diffie-Hellman - the same mathematical basis as modern TLS.
- Session establishment: A one-round-trip handshake generates ephemeral symmetric session keys using the Noise protocol framework.
- Packet encryption: All traffic is encrypted with ChaCha20-Poly1305, a modern authenticated encryption algorithm that performs exceptionally on hardware without AES acceleration.
- Routing: WireGuard uses a Cryptokey Routing table - each peer's public key is associated with the IP ranges that peer is allowed to reach.
What Cryptography Does WireGuard Use?
WireGuard uses a deliberately fixed set of modern cryptographic algorithms, with no cipher agility - you cannot configure weaker options. This is a design choice, not a limitation. It eliminates an entire class of vulnerabilities caused by misconfigured or deprecated cipher selections.
For context on how symmetric and asymmetric encryption differ, WireGuard uses both: asymmetric cryptography for key exchange, symmetric for data encryption:
|
Algorithm |
Role |
Why It Was Chosen |
|
Curve25519 |
ECDH key exchange |
Fast, widely audited, no known weaknesses |
|
ChaCha20 |
Symmetric encryption |
Faster than AES on devices without hardware AES support |
|
Poly1305 |
Message authentication (MAC) |
Authenticates encrypted packets to prevent tampering |
|
BLAKE2s |
Hashing |
Faster than SHA-256 with equivalent security |
|
SipHash24 |
Hash table keying |
Protects against DoS attacks on routing tables |
|
HKDF |
Key derivation |
Derives session keys from the shared secret |
This fixed algorithm set means every WireGuard audit covers the same code path, making independent security reviews more thorough and reproducible.
How Fast Is WireGuard Compared to OpenVPN and IKEv2?
WireGuard is consistently the fastest VPN protocol in controlled tests. Its kernel-space implementation eliminates the context-switching overhead that slows OpenVPN, which runs primarily in user space.
| Protocol | Typical Download Speed | Latency Added | CPU Usage | Code Size |
| WireGuard | 920–960 Mbps | +1–3ms | 8–15% | ~4,000 lines |
| OpenVPN (AES-256-GCM) | 620–780 Mbps | +8–12ms | 45–60% | ~100,000 lines |
| IKEv2/IPsec | 750–850 Mbps | +3–6ms | 20–35% | Varies by implementation |
| L2TP/IPsec | 400–550 Mbps | +10–15ms | 30–50% | Legacy codebase |
Speed figures represent median results from published 2025 benchmark tests on AWS and direct server connections. A peer-reviewed comparison published by MDPI (August 2025) found WireGuard achieved 210.64 Mbps TCP throughput vs. 110.34 Mbps for OpenVPN in VMware environments, according to MDPI empirical VPN performance research (August 2025). Real-world performance depends on server load, distance, and ISP conditions.
Is WireGuard Safe to Use?
WireGuard has passed multiple independent security audits since its Linux kernel inclusion. Its small codebase is its primary security advantage - fewer lines of code means fewer places for vulnerabilities to hide, and the entire protocol can be reviewed by a single cryptographer in a reasonable timeframe.
One frequently discussed trade-off: WireGuard stores peer IP addresses in memory by default. This means the server technically logs which IPs connected, which is a minor privacy consideration compared to the key VPN security benefits it provides. Most commercial VPN providers solve this with a double NAT layer or rotating IP system - NordVPN's NordLynx and Mullvad's WireGuard implementation both address this by design.
Which VPN Providers Support WireGuard in 2026?
WireGuard is now the default or recommended protocol for most major VPN services:
|
VPN Provider |
WireGuard Support |
Implementation Name |
Default Protocol? |
|
NordVPN |
Yes |
NordLynx (WireGuard + double NAT) |
Yes |
|
ExpressVPN |
No - proprietary Lightway instead |
Lightway (similar design principles) |
Yes |
|
Mullvad VPN |
Yes |
Standard WireGuard |
Yes |
|
ProtonVPN |
Yes |
Standard WireGuard |
Yes |
|
Surfshark |
Yes |
Standard WireGuard |
Yes |
|
Private Internet Access |
Yes |
Standard WireGuard |
Yes |
|
IPVanish |
Yes |
Standard WireGuard |
Yes |
ExpressVPN's Lightway protocol uses the same design philosophy as WireGuard - minimal codebase, fixed algorithms, kernel-level processing - but is a separate implementation developed in-house.
When Should You Use WireGuard vs OpenVPN?
WireGuard is the better choice in most situations. The only scenarios where OpenVPN still has a clear advantage are:
- Restrictive firewalls: OpenVPN can run on TCP port 443, making it indistinguishable from HTTPS traffic to deep packet inspection systems. WireGuard uses UDP and can be blocked more easily in countries like China, Russia, and the UAE.
- Legacy enterprise systems: Some corporate security tools and monitoring platforms were built around the OpenVPN certificate ecosystem and cannot parse WireGuard connections.
- Obfuscation requirements: For VPN use in heavily censored environments, some providers offer obfuscated OpenVPN that disguises VPN traffic. WireGuard obfuscation tools exist but are less mature.
For everyday use - streaming, remote work, privacy browsing, mobile connections - WireGuard is faster, simpler to configure, and uses less battery on mobile devices.
WireGuard Has Set the New Standard for VPN Protocols
WireGuard arrived as a proof that a VPN protocol could be both simpler and more performant than the decade-old alternatives. Its inclusion in the Linux kernel was a signal that the security community considered it production-ready, and the subsequent adoption by every major VPN provider confirmed that assessment.
For users, the practical benefit is a faster, more reliable connection with fewer configuration requirements. For developers and system administrators, the small auditable codebase means fewer unknowns in a security-critical component. As post-quantum encryption becomes a priority, WireGuard implementations supporting ML-KEM hybrid key exchange are already in production at providers like Mullvad - making WireGuard the foundation for the next generation of VPN security as well.
Frequently Asked Questions
Is WireGuard built into my operating system?
Yes, for most users. WireGuard is included natively in the Linux kernel (since version 5.6), macOS (via the App Store client), iOS, Android, and Windows 10+. You do not need to install third-party software to use it - your VPN provider's app handles this automatically.
Does WireGuard support all devices?
WireGuard supports Linux, macOS, iOS, Android, and Windows natively. Router support varies - OpenWrt supports WireGuard, and many consumer routers running Asus Merlin or DD-WRT firmware do as well. Older enterprise VPN appliances may not support it without a firmware update.
Can WireGuard be detected and blocked by ISPs?
WireGuard traffic can be identified by deep packet inspection tools because it has a distinctive UDP handshake signature. ISPs and governments in censored regions can block it. If you need to bypass such restrictions, use a VPN provider that offers an obfuscation layer on top of WireGuard, or switch to OpenVPN on TCP port 443 when traveling.
How does WireGuard handle roaming (switching from Wi-Fi to mobile data)?
Exceptionally well. WireGuard's stateless design means it does not need to renegotiate a new session when your IP address changes. The tunnel resumes automatically within milliseconds of reconnecting to a new network - significantly faster than OpenVPN, which requires a full reconnection and TLS handshake.
Is WireGuard free to use?
WireGuard itself is free and open-source, released under the GPLv2 license. You can run your own WireGuard server on a VPS for a few dollars per month. Commercial VPN services that use WireGuard charge their standard subscription prices - the use of WireGuard does not typically change the price relative to providers that use OpenVPN.
What is the WireGuard Noise protocol framework?
Noise is a framework for designing cryptographic handshake protocols with formal security proofs. WireGuard uses the Noise_IKpsk2 handshake pattern, which provides mutual authentication, forward secrecy, and identity hiding. It was designed by Trevor Perrin and has been formally verified by academic cryptographers.